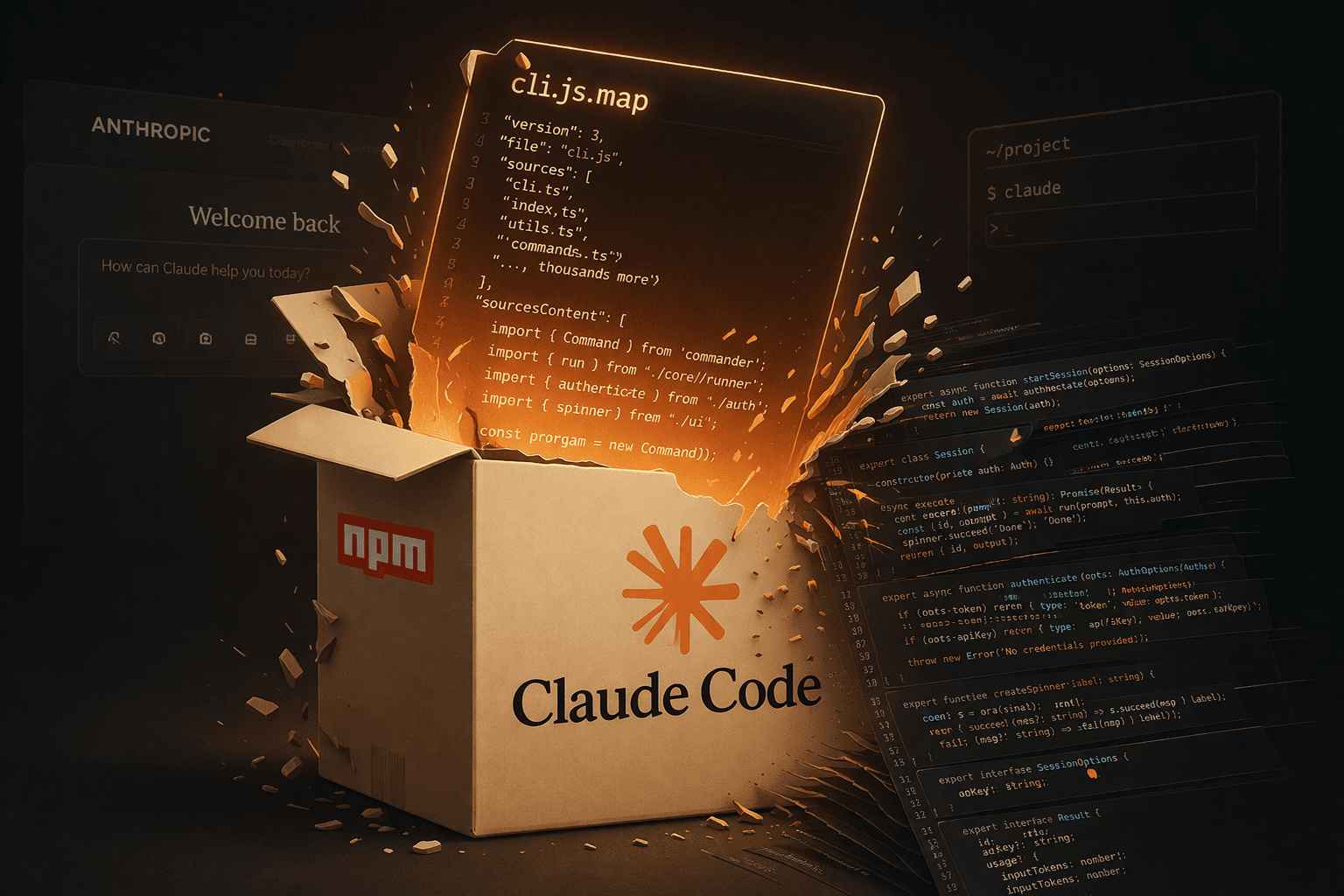
Claude Code Leak via npm Reveals Anthropic Internal Architecture
A major leak hit after the Claude Code tool source was accidentally published on npm, marking one of the most notable AI tooling leaks this year.
In a critical incident, a source map file was included in the official package, allowing a full reconstruction of the TypeScript project behind the CLI tool. Despite the hype, what was exposed is the tool’s source code, not the model, its weights, or any user data.
What Was Actually Leaked?
The leak is limited to the source code of Claude Code, a CLI tool developers install locally via npm to interact with Claude, manage projects, and execute commands.
- Hundreds of thousands of lines of code
- ~1900–2000 TypeScript files
- Client logic, session management, and API integrations
- Telemetry, permissions, and internal security layers
No model weights, training data, or API keys were exposed, as these remain within Anthropic’s backend infrastructure.
How Did the Leak Happen?
The issue was caused by a release mistake, where a sourcemap file was included in version v2.1.88:
cli.js.mapThis file, typically used for debugging, contained enough information to reconstruct the full original source code. It was extracted and published on GitHub, with multiple mirrors appearing within hours, making containment nearly impossible.
Notably, this is not the first time—similar incidents were reported in 2025, raising concerns about release practices.
Why This Is Not “Claude Itself”
The leaked code represents the client and orchestration layer, not the AI model itself.
- Handling developer commands
- Managing sessions
- Executing commands in isolated environments
- Applying security policies before API calls
The Claude model, its architecture, and training data remain untouched and cannot be derived from this code.
What Does the Code Reveal?
- Design of agent-based (agentic) systems
- Sandboxing and secure bash execution
- Internal task orchestration logic
- Telemetry and developer behavior tracking
This makes the tool highly valuable for both security researchers and competitors.
Real Impact
There is no direct risk to users, but the bigger impact is on the company itself:
- Exposure of internal security architecture
- Easier vulnerability discovery
- Competitive disadvantage
- Reduced trust in software supply chains
Why Do These Mistakes Happen?
- Weak release review processes
- Poor separation between dev and production environments
- Lack of strong CI/CD security checks
What Does This Mean for Developers?
- Avoid blind trust in published packages
- Audit dependencies before use
- Do not run untrusted tools with full permissions
Conclusion
This incident highlights that risks are not limited to AI models themselves, but also the tools built around them. It reinforces the importance of secure release practices and thorough package validation.